Installing Magento 2.4.3 Community Edition on a Windows machine and deploying on the localhost
Boring but useful. Magento is an ecommerce platform that many use for their online sales. Installing it can be tricky though and here’s a tutorial to practice installing it locally before pulling the trigger to deploy it live.
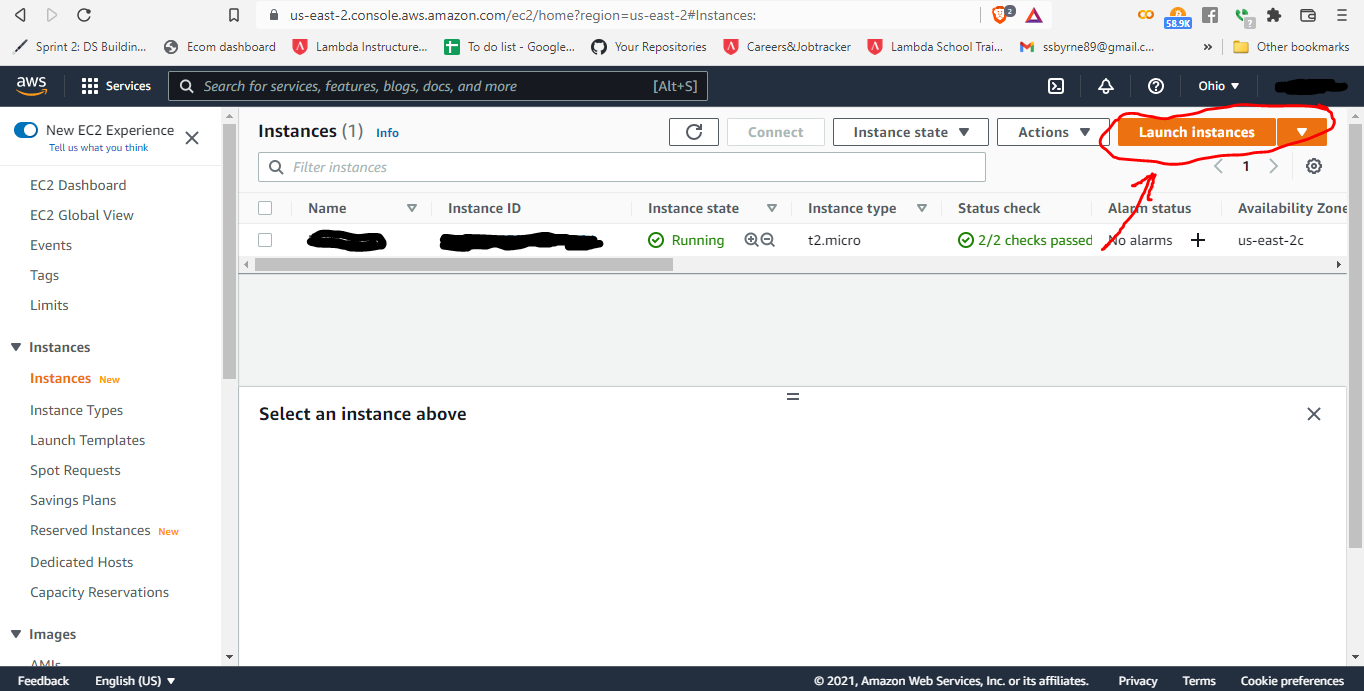
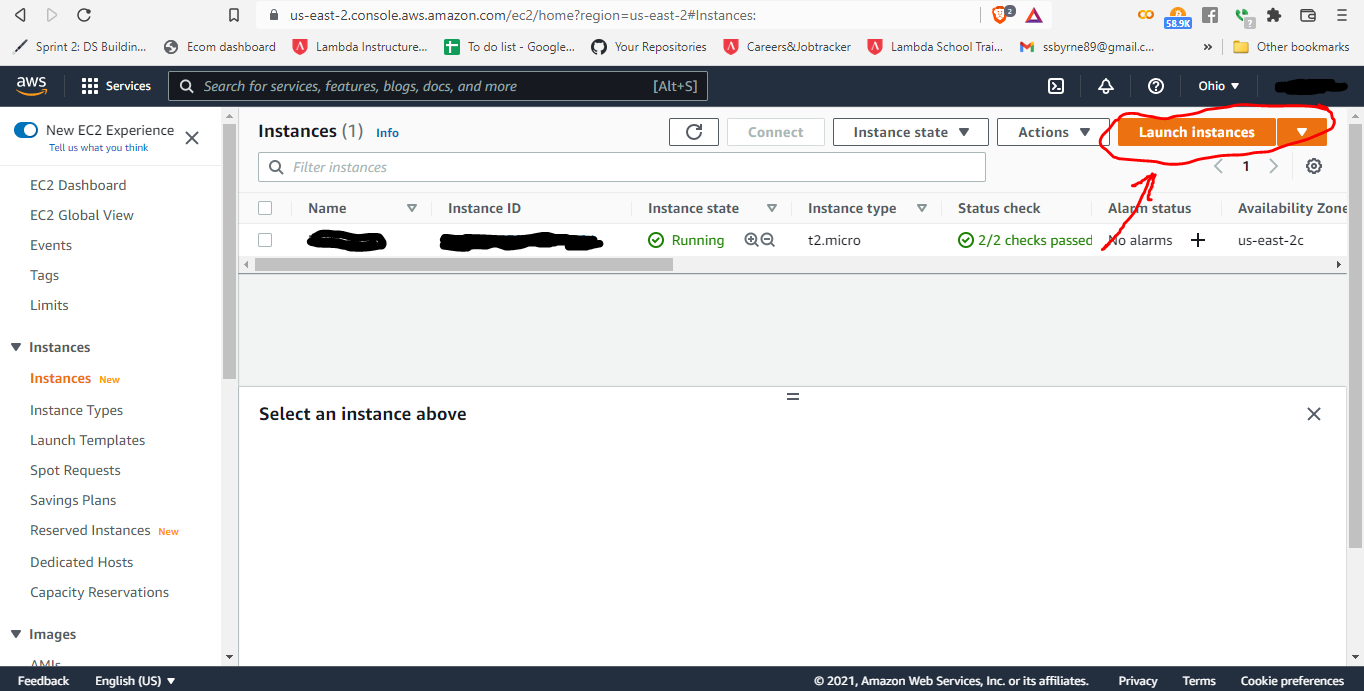
Deployment of a Magento 2 Website on a Remote AWS Server
It took quite a while for me to dial in this process, even referencing the documentation and dozens of online tutorials. Anyway, I hope some of you can avoid some of the trials and tribulations I faced by using this as a reference.

MAC Address Spoofing and YOU!
What is a MAC address? What is MAC address spoofing? How it’s good. How it’s bad. You’re going to want to sit down for this one… I reference an academic article

Virtual Machines, Virtualization, and Using This Stuff for YOUR Own Personal Cyber Security
Some might find this interesting. This will cover how to use software that malicious hackers use, but for your own personal security!

How to Manually Change Your MAC Address and a Teeny, Tiny, Simple, Little Python Algorithm to Do It for You on Linux or Apple Operating Systems
Don’t worry Windows users, I throw a bone in here for y’all, as well 😉

Let's Go ARPing!
Some might argue that saying the word out loud is actually the only entertaining thing about ARPing.

How to Code a Network Scanner to See If Anyone Is Camping-out on Your Wi-Fi
Do you suspect some peeping-toms on your your Wi-Fi? I’ll break down this python function that uses Scapy to scan your network for devices on your Wi-Fi.
Man-in-the-Middle, ARP Spoofing???
What is all this weird terminology? Are these cultish sex positions, or something? Nah… just techy jargon, but there will be a demonstration at the end ;)

Backing Up Your Website’s Files: A Quickie How-to Guide
This one thing could save your buns thousands of dollars!!! How’s that for a clickbait-y title?

Lemme Sniff Yer Packet!
Packet sniffing and your amazon delivery person… just kidding. I’m talking about digital packets sent to devices over Wi-Fi networks

DNS Spoofing: Part Deux
A little more info on data packets, the DNS layer and what fields to check if you suspect spoofing!

Terminal Commands: A Reference
A listicle of commands to run in a terminal and navigate directories and logs like a pro! Mostly for Linux but some of them work in Windows also.

All of the Malware
What is malware? What types of malware exist? Better find out because it’s inevitable!

Security Applications and Devices
Check this one out! All about the software and hardware you can use to keep the digital nasties from infecting your machines. Digital hygiene should be up there with sexual hygiene in terms of importance, so don’t be a fool and wrap your tool!

Let's Get Physical
Shall we discuss the differences between Olivia Newton-John’s version of Physical and Dua Lipa’s version of Physical? As much as I would love to, alas, that won’t be what we’ll discuss. Instead we’re going to cover something much less interesting and that is the physical aspects of cybersecurity.

So, you want to be a cybersecurity professional?
An Overview of Security along with the Basics and Fundamentals according to the CompTIA Security+ Certification Exam
I'm summarizing the CompTIA certification because it is one of the more widely recognized certifications amongst employers.

Mobile Device Security
This is exactly as it sounds. If you're reading this article on your phone, tablet, laptop, etc… then this is surely relevant to you. If you still use a pager then you can skip this one. Anyway, we’ll cover what threats we can expect and what we can do to protect ourselves.

Hardening
Yeah, I agree. This term sounds funny, but get your head out of the gutter. It actually has to do with improving cybersecurity.

Can I use penicillin on my malware infection?
No, you cannot. Malware is like herpes: lurking everywhere and anti-biotics can’t kill it…YIKES! When it comes to malware, best to learn how it can be prevented. So, we’ll cover identification and prevention as well as how it’s covertly installed on our machines. Also, it’s super handy to be able to recognize symptoms of infection. Plus tips on malware removal!

DNS Spoofing
How They Get Between YOU & YOUR Internet Connection to Change What YOU See!

Facilities Security
Spoiler alert! This will not cover fences.